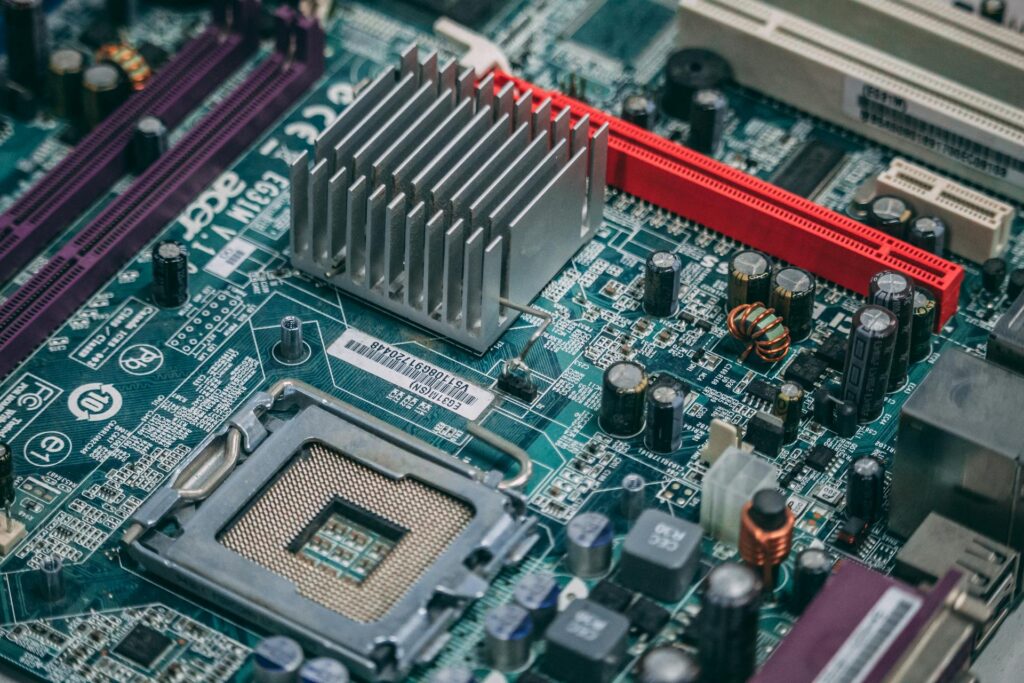
Every device that accesses business systems represents a potential security risk if not configured correctly. Computer One’s Device Configuration & Security services ensure that laptops, desktops, and mobile devices are set up with consistent security controls and policies.
By standardizing device configuration and enforcing security settings, we help businesses reduce risk, protect data, and maintain control across all endpoints.
Misconfigured devices are a common cause of security incidents and performance issues. Without consistent configuration standards, devices may lack essential protections or expose sensitive data.
Without proper device configuration and security, businesses risk:
Our services focus on standardization, protection, and control.
Devices are configured using consistent security and usage standards.
Access controls and security settings are applied uniformly.
Settings help protect business data stored or accessed on devices.
Devices are monitored for adherence to security policies.
Consistent configuration reduces vulnerabilities and exposure.
Standardized configuration ensures every device meets minimum security requirements. Consistency reduces gaps that attackers often exploit.
Uniform security improves overall protection.
Improper settings can leave devices exposed. Device configuration services eliminate misconfigurations that lead to vulnerabilities.
Reducing misconfiguration lowers incident risk.
Centralized configuration provides visibility into device status and compliance. Better visibility supports faster issue resolution and enforcement.
Control strengthens endpoint management.
We support a wide range of endpoint environments.
Configurations prioritize data protection and control.
We simplify device security oversight.
Device security aligns with MDM, support, and cybersecurity services.
Our solutions help future proof your business by ensuring your data is always secure, accessible, and recoverable in any situation.
Grows with your business and adapts to evolving data needs.
Keeps sensitive information protected at all times.
Can’t find the answer you’re looking for? Please chat to our friendly team!
Changing IT companies might feel intimidating but it doesn’t have to be. We’ll guide you every step of the way and handle the hard parts for you.
We’ll show you what stress-free technology really looks like.
337‑233‑9245
Serving Louisiana and Southern Mississippi